Summary
This note presents a number of easy steps to circumvent the entry every ten minutes of a 2FA PIN-code on Exact Online when used with Invantive Control for Excel, Invantive Query Tool and other on-premises interactive Invantive apps.
For console apps running from the task manager or crond such as Invantive Data Hub and Invantive Data Replicator, please refer to Circumvent two-step verification and refresh tokens on Exact Online using Data Hub.
The following steps can be used with or without Invantive Authenticator:
https://two-step-verification.solutions
Circumventing 2FA poses an only limited additional security risk since connected apps using Code Grant Flow can already work without a PIN-code after initial entry, using an OAuth2 refresh token.
Update 2020
Exact has added the requirement that a refresh token has a limited lifetime of 10 minutes when in use. Later in 2021 they might enforce the condition that a refresh token expires after 30 days when stored but not used. This increases security from the point of view on Exact, but off-loads the risks towards the local deployment of an app. It remains to be seen whether the weighted security risk shows a considerable improvement.
Update 2021
Exact has added the requirement that the by design short-lifed access token can not be acquired more often than once every 9,5 minutes. This requirement is slowly implemented in all Exact Online countries. In the Netherlands as of November 13, 2021, a minimum interval between access token acquisitions holds of 10 seconds.
Update Oktober 2024
Note that with the introduction of Azure B2C as part of One Exact Identity two-step verification has effectively been made irrelevant for many months, as a single log on in a country allows log ins from other IP-addresses and devices in that country without proving possession of the token generator by entering the then current verification code.
Exact Online 2FA and Invantive Control for Excel
Starting May 25 2018, Exact Online is requiring the use of 2FA for all users. When properly implemented, you can achieve strong authentication with 2FA on Exact Online. Strong authentication is required by law for reasons such as irreversible financial transactions and data traceable to individuals. For a proper implementation, you must isolate the storage of the secret used to generate the 2FA PIN-code from your normal working environment. Generating the 2FA PIN-codes on a mobile phone achieves this largely. This is similar to the Vasco hardware tokens previously used by Exact Online, but these came with a charge of EUR 5 per hardware token per month.
There are many apps available on Exact Online. Some apps apply the so-called “Implicit Grant” in adherence to the OAuth recommendations. This typically holds for apps running on devices untrusted by the owner of the application, such as Invantive Control on your PC or an iPhone app.
However, at this moment the use of Implicit Grant also requires you to re-enter a new PIN-code every ten minutes. For Invantive and other app suppliers there is no supported way of avoiding this hassle during your use of our applications. This note presents a number of easy steps to circumvent this problem.
Jump directly to the steps to execute or continue reading the background.
Additional security recommendations for Exact Online can be found in another post.
** Update 2022 **
Using client secret is again possible with Invantive Control for Excel; see Register Exact Online app for use with Invantive Control for Excel.
How 2FA Works
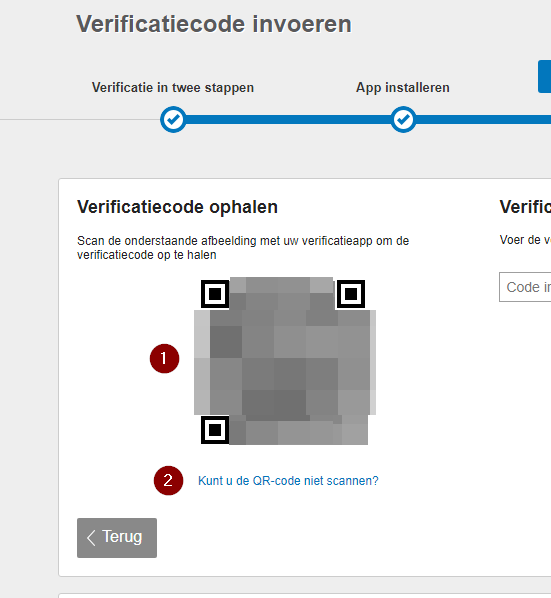
The implementation of Exact Online is based upon an industry standard for Time-based One-Time Passwords (TOTP). During the TOTP registration, your mobile device or chosen program exchange a shared secret. This shared secret is contained in the QR-code on the TOTP registration page:
The QR-code next to the red has been completely blurred since a QR-code is extremely insensitive to transmission errors. Truly a miraculous algorithm made by mathematicians.
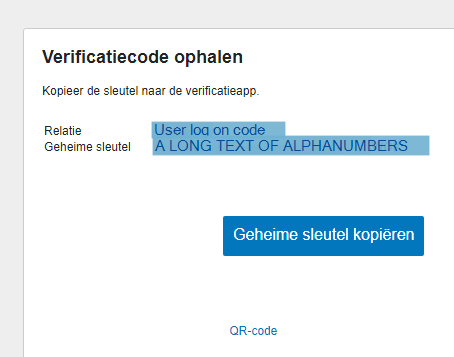
Using this QR-code, the Exact Online app shares a secret like the following with your phone:
otpauth://totp/ExactOnline%3aMYLOGINCODE?secret=ALONGTEXTOFDIGITSANDCHARACTERS&issuer=Exact%20Online
This secret can also be seen when you click on “Can’t scan the QR-code” at the red below the QR-code:
An algorithm takes the pre-shared secret and the current world time rounded down to 30 second precision and calculates the PIN-code. This PIN-code calculation takes place at both ends of the communication: at the side of the user and at the side of Exact Online. A user is allowed access when both entries match.
Such a pre-shared secret can also be used with Invantive Authenticator as shown in this video:
It is either very hard or impossible to derive the pre-shared secret even with a large number of PIN-codes and associated timestamps available.
Alternative implementations found in the cloud market do not share the secret with you, but put the secret keys on a closed environment to which the user has no access. This closed environment upon user request communicates the PIN-code to you using a separate channel such as SMS (preferably, such as Dropbox) or mail (well… sometimes an attack vector).
Generate a new Exact Online QR-code
If you haven’t saved your current Exact Online QR-code, and thus cannot extract the Secret Key, you can generate a new QR-code.
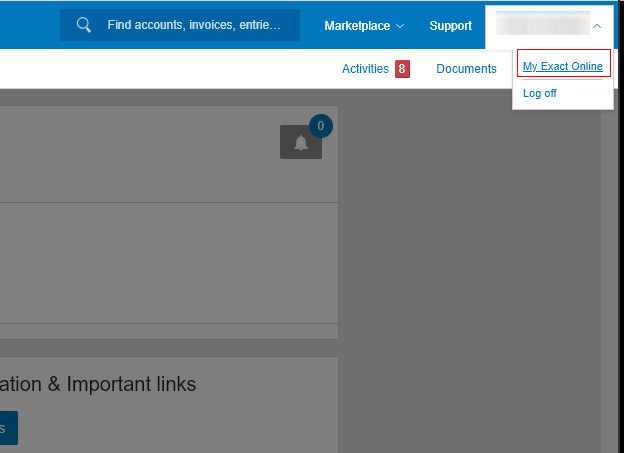
Log on to Exact Online, click on your username in the top right corner and select “My Exact Online”:
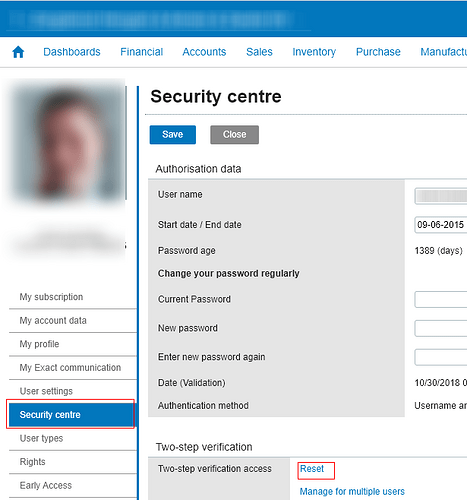
Now click on “Security centre” in the menu on the left and then click on “Reset” under the Two-step verification header:
This will get you back on the TOTP registration page, you can now click “Can’t scan the QR-code” to get the Secret Key and scan the new QR-code with your desired application and store and use the Secret Key as described above.
Circumvent Exact Online 2FA for apps
New releases of Invantive applications for running on your devices support two additional approaches to log in on Exact Online:
- Using a refresh token, client secret, client ID and redirect URI.
- Using the user, password and pre-shared TOTP secret.
Log in using Refresh Token
Although all our products support for use on your devices support both approaches, we recommend the use of a refresh token with server-oriented products like Invantive Data Replicator or Invantive Data Hub. These products typically run unattended on a server using a dedicated Exact Online account. Contact our support to upgrade and together generate a client ID, client secret and refresh token using the pre-authentication site cloud.invantive.com.
Please store your credentials carefully, since they allow access to your Exact Online data with the same privileges as the user. Also, subsequent assistance is only offered based upon a consulting rate. As an alternative, you can generate a new refresh token using the documentation.
Server products such as Invantive Data Access Point have come to support Exact Online 2FA too, both for normal use as well as with Ajax, but they require the use of your own client ID and secret. If you base an application on Invantive products, please ALWAYS make sure you either DON’T persistently store refresh token or store them encrypted according to the law.
Log in interactively using TOTP Secret
You should perform the following steps to log in to Invantive Control and other interactive apps using the credentials of your user account:
- Re-generate the QR-code and click on the red as shown above or extract the secret key from the QR-code image otherwise using a trusted decryptor.
- Store the TOTP secret key under lock & key and consider it part of your password.
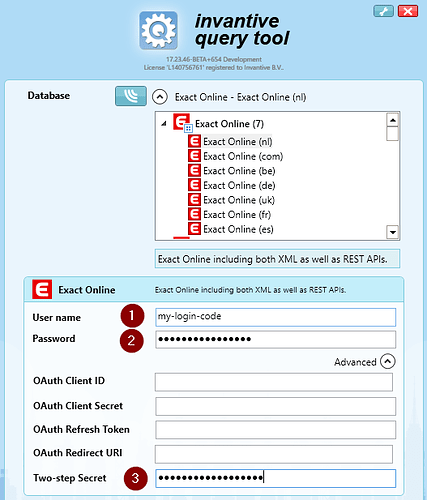
- Upon log in to Invantive Control, provide your user name, password and secret TOTP key in the login box:
- Note that the TOTP-secret key can currently be stored unencrypted on your device in
settings.xml. Therefor ensure application of other security measures such as using the device only inside a secured building or protect access to Windows by a log on code and password and hard disk encryption. We will improve this mechanism in a future release. - Note that Exact Online as far as known does not impose location-based access controls on all apps and interactive use. Store your credentials safely and use them only in trusted environments with trusted apps! Check that the apps you use are provided by suppliers located within your own legislation region (country or European Union as long as that still holds) or considered comparable with your legislation and in which law is actually enforced.